In the last two articles, we looked at seven seemingly innocuous situations and what was really happening. Now, we’re going to look at how scammers are still profiting from our basic trust in others, and what we can do about it.
First though, don’t feel bad if you’ve been the victim of a scam. I dare say it’s happened to all of us. It’s certainly happened to me. Scammers send out millions of email and text messages; impersonate millions of people; post millions of times on social media sites; and have vast networks of their own to create fake profiles and pages, and sell tidbits of information that are later compiled into complete portfolios of real people.
Because they are so prolific, they only need a few people to be fooled by each “project.” And that’s the main reason that we are fooled. Because a few of us do know someone named Maggie Jones, and a few of us did post photos to Facebook earlier today, and most of us don’t want to send a message back to a parent or boss saying, “How do I know it’s really you?” when the message came from their own account. And, as the previous article demonstrated, these internet pirates are getting more sophisticated and are using more personal information to target individuals. So, how do we thwart these criminals? Here are a few tips.
Be mindful of what information about you is available to the public. For example, our website gives the names and job titles for everyone at Internet Advertising. If I get an email late one night from James saying that he accidently deleted his password for a site he has to have finished by morning, my first instinct is to send him mine. But, what I should realize is that anyone would know that we’re colleagues, so I need to make sure the message is actually from James.
Understand that it may not have been you who got hacked. If anyone of your friends on Facebook inadvertently gave someone their credentials, the scammer can now see your feed. Be particularly cautious of posting information about your children, the school or dance academy they go to, when you’re leaving on vacation, etc. Post those cute holiday pics after you get home.
Know that information about you is being compiled. Limiting your personal social media accounts is one way to reduce the amount of info that scammers can collect from different sources. Do you really need accounts with Facebook, Twitter, Instagram, SnapChat, Google, WhatsApp, YouTube, Yammer, Bebo, Pinterest, Reddit, and Flickr? The data being collected about you now also includes your interests, what you like, how you feel about politicians, recording artists, etc., etc. It’s valuable to marketers.
Change your email settings to not send immediately. It is very easy to spoof an email address, and in many cases the only way to check that it’s the address you think it is, is by replying. If you are able to change your email settings to not send immediately, (in Outlook, go to File, Options, Advanced, Send and receive, and make sure the “Send immediately hen connected” is not checked), then you can prepare your response, click Send, then go to your Outbox and see what addresses it shows. Here’s an example:
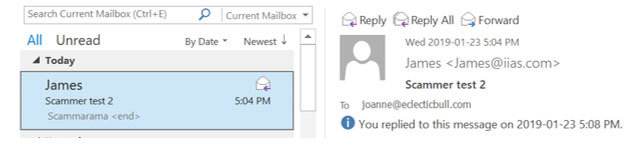
This image shows the message I received from the spoofed James account. It shows that it came from his actual email address.
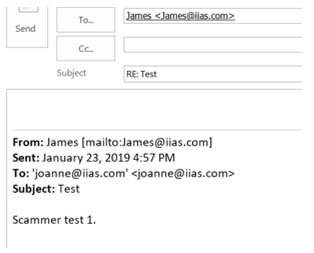
Even when I click Reply, it shows that the message is going to James actual email address.
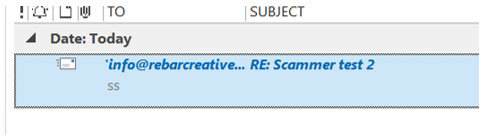
But when I go to my Outbox, it shows that the message I thought I was sending to James, is actually going to a totally different person.
If you can’t change the settings and are at all suspicious, reply with a test message; e.g. “Give me 5,” then go to your Sent Mail folder and look at the address you just sent to.
Be suspicious of any message that asks for information or contains a link. Scammers use urgency, fear, and playfulness to try to trick us into taking action. They’ll also use the information that’s been compiled about you, your colleagues, and your family to add a familiar touch or try to scare you. In the early days, these scam messages had tell-tale signs like poor spelling, bad grammar, or fuzzy images. Some still do, and that’s a tip off, but many others appear to be legit. So, whether it’s an email message, a text message, a private message on social media, or even a post, if there’s a link, a request for login info or money, double check with who you think the message is from before doing anything else.
Don’t get sucked into “challenges.” And warn your kids and parents! One’s like the cinnamon or salt and ice challenges are downright dangerous. The newer “ten year challenge,” that asks you to post two photos of yourself, ten years apart, is suspected to be a huge data collection scam.
Use all of the tools available to you. Spend the money to purchase a security program from a reputable source. A free one could attack you itself. Turn on automatic updates for your operating system and software programs. Close any social media accounts that you don’t use at least weekly, and delete any apps you no longer use. Don’t share your login credentials, and if you feel you have to, do it by telephone. Take a minute to think, and trust your gut. Even if the message is urgent, give yourself time to process and consider the consequences if it is a scammer.
Do you have a tip for spotting scammers? Let us know, and we’ll we share it.


